Notes from the author: I want you to understand what is asked of a SOC analyst and what they do and how they do it.**
*I hope this article can aid you in not just becoming one but a great one.*
What is the Role of a SOC Analyst in Cybersecurity?
In today’s digital landscape, cybersecurity has emerged as a paramount concern for organizations worldwide. Security Operations Center (SOC) Analysts play a pivotal role in this domain, dedicated to monitoring and safeguarding an organization’s IT infrastructure, networks, and data. Working within a Security Operations Center, these analysts address security issues at both organizational and technical levels, actively identifying, analyzing, and responding to security incidents to ensure the prompt detection and mitigation of potential threats, thereby maintaining the integrity and confidentiality of sensitive data.
Vigilance is not merely a creed but a responsibility for Security Operations Center Analysts, whose primary goal is adept identification using tools to monitor networks, systems, and applications. Any signs of unusual activity or potential security breaches serve as a call to arms, prompting analysts to delve deep and mitigate or halt such occurrences altogether. This task is facilitated by leveraging tools with scrutiny and a comprehensive understanding of cybersecurity and information technology fundamentals.
Upon identifying a threat, SOC analysts embark on an investigative journey, utilizing tools tailored to the situation to uncover threat vectors and piece together a timeline and scope of the incident. This forensic examination provides valuable insights, allowing for the implementation of enhanced defenses against future attacks.
Once an incident requiring a response is identified, SOC analysts pivot to deliver decisive action, formulating strategies to contain, mitigate damage, and neutralize the threat. Whether it involves isolating compromised systems, blocking malicious IP addresses, or deploying patches and updates, precision execution is paramount in this battle, where swiftness is crucial for effective damage mitigation.
Preserving organizational integrity and confidentiality is paramount for SOC analysts. Through promptly detecting and mitigating potential threats, they safeguard sensitive data from malicious actors. This is achieved by much of the following:
*It should be noted that this is not every single thing a SOC analyst does but it will allow anyone to understand what they do.*
The Core Responsibilities of a SOC Analyst
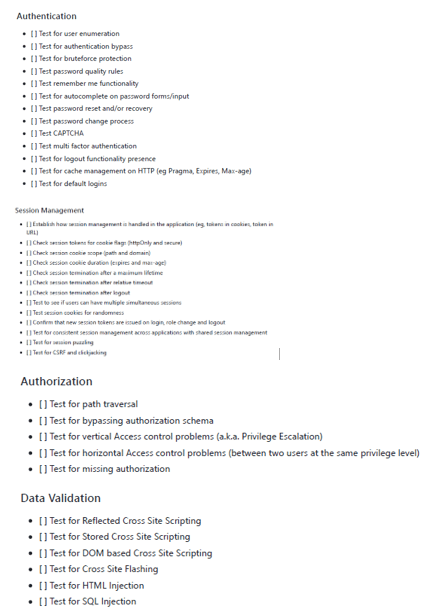
SOC analysts utilize a variety of security tools and technologies, such as Security Information and Event Management (SIEM) systems, intrusion detection systems (IDS), and firewalls, to uphold the organization’s security posture. By analyzing security alerts and recognizing patterns of suspicious activity, they leverage their expertise to assess the severity and potential impact of security incidents. Staying updated on the latest cybersecurity threats and trends, SOC analysts contribute to both proactive and reactive defense strategies of their organization.
Some things you will be asked to do as a SOC analyst: Monitoring and Detection: Continuously monitoring network
traffic and system logs to detect security threats.
Incident Response: Quickly responding to security incidents,
conducting thorough investigations, and implementing effective solutions.
Compliance: Ensuring that the organization’s security
measures comply with relevant regulations and standards.
Documentation: Assisting with building, auditing, and
documenting secure IT infrastructures.
SOC analysts must possess strong analytical and
problem-solving skills, enabling them to investigate incidents thoroughly and recommend effective solutions. They also need a comprehensive understanding of networking concepts, operating systems, and cybersecurity principles. Proficiency with security tools and technologies such as firewalls, SIEM, IDS/IPS, and antivirus software is essential. Awareness of common cyber threats, attack vectors, and mitigation strategies further enhances their ability to protect the organization.
Technical skills developed and tools used while being SOC analyst include:
Networking and Protocols: Excellent knowledge of TCP/IP,
UDP, DNS, FTP, SSH, SSL/TLS, and HTTP protocols.
Security Solutions: In-depth understanding of technical
security solutions like firewalls, SIEM, NIDS/NIPS/HIDS/HIPS, AVs, DLP, and
proxies.
Threat Analysis: Ability to analyze and respond to undisclosed software and hardware vulnerabilities, and investigate, document, and report on emerging trends.
Scripting Languages: Proficiency in scripting languages, particularly Microsoft PowerShell, to automate tasks and improve efficiency.
Digital Forensics: Using such tools as Autopsy, EnCase Forensic, Sleuth Kit, Volatility, Wireshark, Splunk, Endpoint Security just to name a few.
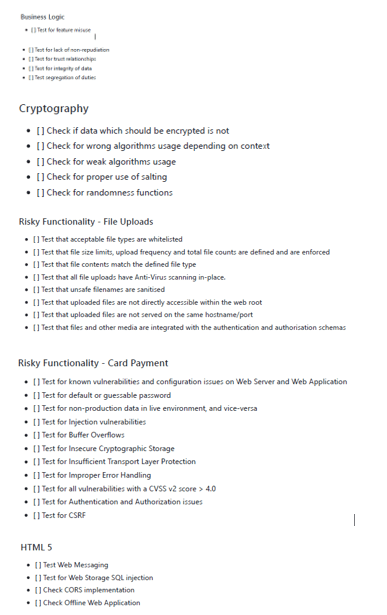
Compliance and Regulatory Bodies
Compliance and regulatory knowledge are standards in cybersecurity being set by local, state, federal and otherwise for us to follow. Being a Security Operations Center analyst does not exempt anyone from such standards, in fact you supposed to be an expert when it comes to such things.
SOC analysts play a crucial role in ensuring that their organization’s security measures comply with various standards and frameworks. This can be called compliance and regulatory knowledge.
I will go over a few with only brief descriptions below:
FedRAMP: Federal Risk and Authorization Management Program.
NIST 800-53: National Institute of Standards and Technology’s guidelines for security controls.
ISO/IEC 27001: International standard for information security management.
GDPR, HIPAA, PCI-DSS, SOX: Compliance with regulations like the General Data Protection Regulation, Health Insurance Portability and Accountability Act, Payment Card Industry Data Security Standard, and Sarbanes-Oxley Act.
By understanding and adhering to these standards, SOC analysts help organizations maintain a strong security posture and avoid potential fines and legal issues.
Certifications
Certifications sought out by SOC analyst employers and themselves. As a SOC analyst it should be a goal to expand and test your knowledge in cybersecurity. Certifications are a topic for a whole article, but they should be on the horizon for a cybersecurity professional at the very least. While not always mandatory, certifications can significantly enhance a SOC analyst’s qualifications and credibility. Preferred certifications include:
Palo Alto Networks Certified Cybersecurity Associate (PCCSA)
Certified Information Systems Security Professional (CISSP)
CompTIA Security+ and Cybersecurity Analyst (CySA+)
Certified Ethical Hacker (CEH)
Certified Information Security Manager (CISM)
Experience with SIEM and SOAR platforms, preferably Splunk
or Google, is highly valued, along with a strong foundation in scripting
languages like Microsoft PowerShell.
Cybersecurity Initiatives and Continuous Learning
SOC analysts are also key contributors to broader cybersecurity initiatives within their organizations. Their roles often involve:
Information Assurance: Ensuring that information systems are protected against unauthorized access and other threats.
Network Security: Implementing measures to secure network infrastructure and prevent data breaches.
Data Analytics and Machine Learning: Using advanced analytics and machine learning techniques to detect anomalies and predict potential security threats.
Cyber Response: Developing and executing response plans to mitigate the impact of security incidents.
Continuous learning is essential for SOC analysts to stay ahead of emerging threats and evolving technologies. Participating in training sessions, attending cybersecurity conferences, and obtaining advanced certifications are vital for maintaining their expertise.
Being a member of a Team
SOC analysts are commonly utilized in team settings as a need for them to be available to provide 24/7 coverage of a system is again common. Workload distribution is also important as this role is if you haven’t realized, extensive and can be far too cumbersome for an individual to perform.
SOC Analysts the Guardians of Cyberspace
SOC analysts are the frontline defenders of an organization’s cybersecurity framework. Their expertise in monitoring, detecting, analyzing, and responding to cybersecurity threats is indispensable in today’s digital world. By staying updated on the latest threats and continuously improving security measures, SOC analysts help organizations maintain a robust defense against cyber-attacks. Their role is not just technical but also strategic, ensuring that security policies comply with evolving regulations and standards, ultimately protecting the organization’s valuable data and infrastructure.
Youtube resource mention
A great resource on YouTube is a channel named Cyber
Platter. There are extensive videos to prepare for SOC-related interviews and certifications: Cyber Platter YouTube Channel.
Even More Resources!
Join Tier 1 at LetsGoIT Patreon to gain access to the LetsGoIT Discord where you will have access to a wealth of learning materials tailored to illuminate the essentials and commonly used tools in various cybersecurity job roles. Visit LetsGoIT Patreon to join and delve into the resources available.