Through authentic discovery, I have grown familiar with the presence of Cyber Commandos of the civilian variety. Some resemble militants while others are very much aligned with stereotypical hacker images.
*These commandos operate on their own volition*
The commandos may offer services that are valuable to those who have copyright material or intellectual property for some reason, or another has been put in areas of the web that are highly accessible or freely accessible to anyone. Sources are easily operated within by average computer literate or illiterate users. These commandos make it inaccessible for anyone not accessing this material through the owner’s approved method. This can result in securing cash flow to the owners and negating theft or sharing of their material. It is notable that the material owners are sometimes powerless to the distribution of their work. If it’s on the internet, then it can be shared or stolen. That is why cyber commandos are employed.
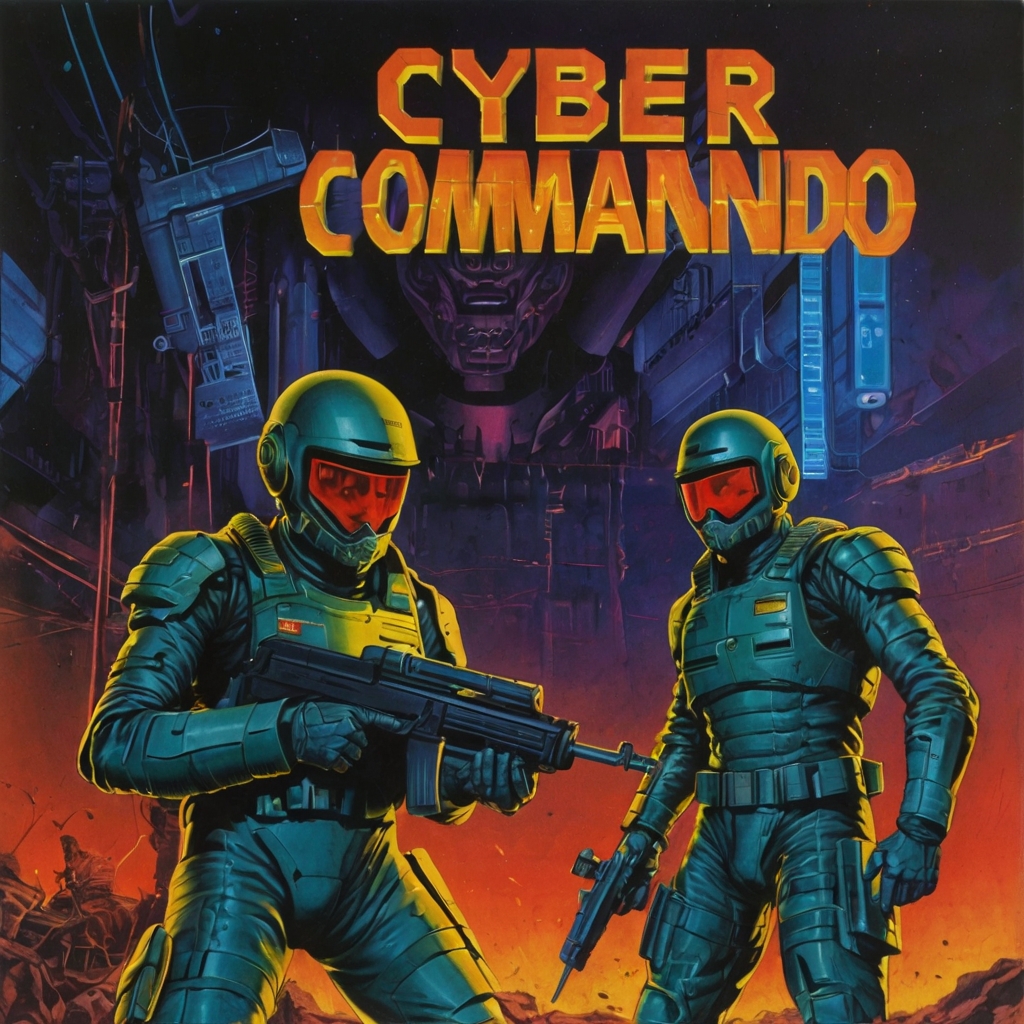
*Their Image*
The image of a Cyber Commando is very important to them, you will not find a lack of militant equipment; it can be summed up with the aesthetic of warxcore but for those of us who are not privy to such terms. The fatigues of a mercenary sums it up rather nicely and they are often equipped with such equipment. Exceptions to this rule are that some cyber commandos operate as hacktivists and that brings with it a different uniform. Their image remains important, it can be the resume or cv of the commando, a bravado borne from the operations they conduct and the clients they have.

*Why have such an image?*
This creates anonymity for the Cyber Commando and such an image can be intimidating to those whose monetary flow is disrupted by their services. Adding a layer of protection or intimidation for their clients benefit.

*Ethics*
A Cyber Commando can navigate a complex ethical landscape in their efforts to secure copyrighted intellectual property. While their mission may be justified, their methods can sometimes blur the lines between ethical and unethical behavior. For instance, they might use social media to identify and target individuals wrongfully possessing copyrighted material, employing aggressive or morally questionable techniques to neutralize these threats.
The role of a Cyber Commando often resembles that of a digital mercenary, where decisions must constantly be weighed against their personal moral compass. Balancing the need to protect intellectual property with the imperative to avoid unethical practices is a challenging aspect of their work. Ultimately, the ethical stance of a Cyber Commando is shaped by their individual values and the choices they make in the face of these dilemmas.
–
*Marketing*
Cyber Commandos market themselves on social media either through direct messaging or referrals by past clients. They can also be found in less than savory locations on the web in forums where more clear mercenary work is advertised. This service is highly sought after by content creators whose products and content are only accessible behind a pay wall

*What do they do?*
Cyber Commandos participate in a few services while skimming ethical boundaries such as getting copyrighted content off popular web resources with DCMA claims that are in place to protect us all.
Tracking down unauthorized social media profiles that depict an individual’s stolen identity. Then getting them taken down by any means to which can produce an immediate effect.
–
*Who do Cyber Commandos piss off?*
Scammers, Conman, and all-around web-based tricksters.
–
*Why use a cyber commandos service*
If you are an individual that produces social media content and content that is behind a paywall you could benefit from such services rendered by a Cyber Commando.
from being used against their interests, which is making money for the most part and this also can aid in protecting others from being catfished! By using the same content to steal from or lead on victims.
You should be aware that using a cyber commandos services can be essentially hiring a mercenary to do your bidding even though the techniques used have potential to be ethically sound; still run the risk of them committing crimes on your behalf.
*That would be Illegal*
–
*If you or someone you know are looking for such a service provider I cannot give you that information: these services run on the line and are often times the commando resorts to unethical social engineering or flat-out intimidation that often only comes back to hurt the client.*
–
*Cyber Commandos that conduct passive operations that produce outcomes that are legally sound and ethical are essentially a white hat with a cooler look but when any line is crossed they have now become another HaaS (hacking as a Service) thug.*

Still serious about utilizing such services or find yourself in need of them :
Reach out to your local police department and begin a case
Offer the information of your adversary to the FBI through the web crime portal >here<
Make a claim to the IC3 internet crime complaint >here<
*Keep in mind that a cyber commando is typically utilizing protections that are already available to us all please become aware of the DCMA Guidelines for further explanation* https://www.copyright.gov/dmca/